Exporting and Printing
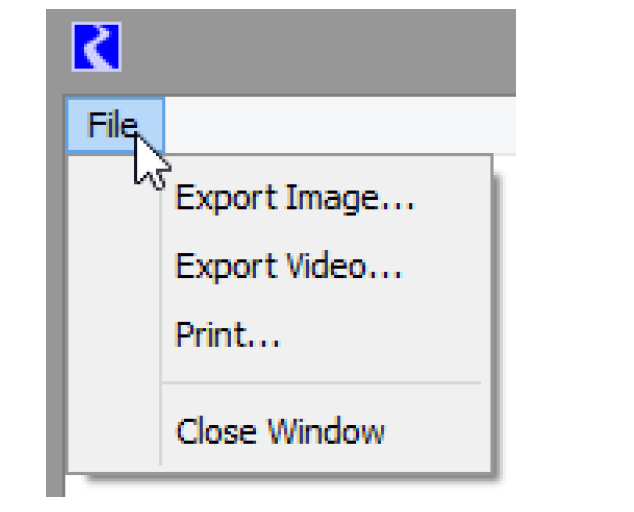
The File menu at the top of the chart display allows the chart to be printed or exported as an image or a video.
Note: When the chart display is printed or saved as an image, the File menu and the date spinner, if present, are hidden. The resulting graphic then shows the date beneath the subtitle. Within the configuration, you can specify the color of the chart background for export and printing. The default is white. See Configuring Charts for details.
Export Image
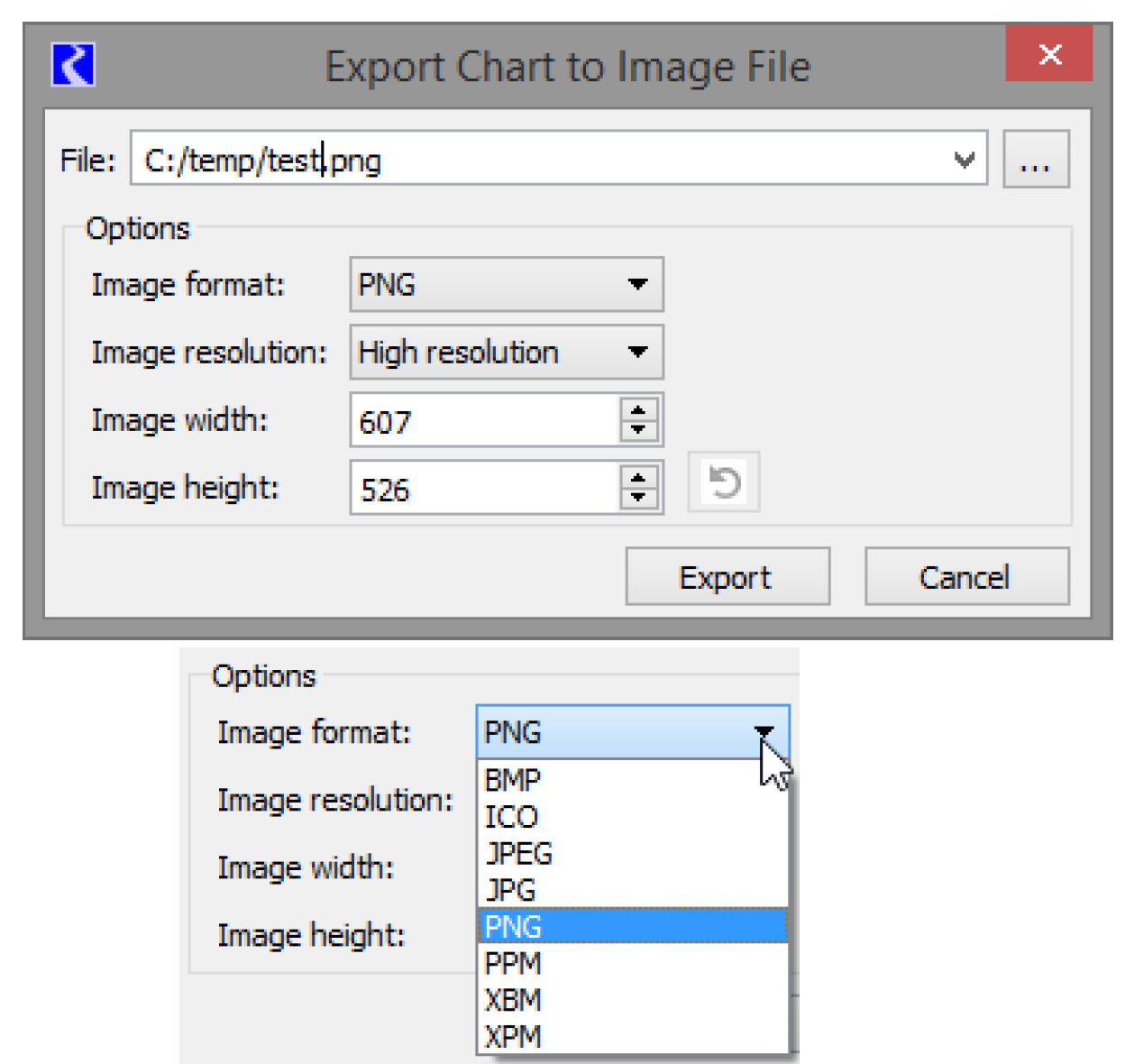
Select Export Image to export an image of the chart to a file. Figure 5.10 shows the Export dialog. Specify the File name and modify any configuration options.
Eight different image formats are available for saving the image file, as shown in the bottom part of Figure 5.10. Resolution and sizing options are also provided in the configuration.
Figure 5.10
Print Image
Standard print options are available to select a printer and then configure the printer.
Export Video
Use the Export Video menu to generate a video file of the chart animation.
This tool works by creating images of the chart at specified intervals as the chart is animated. The images are then combined into a movie file using an external process. You have control over both the sampling of the animation and the creation of the output file.
Figure 5.11
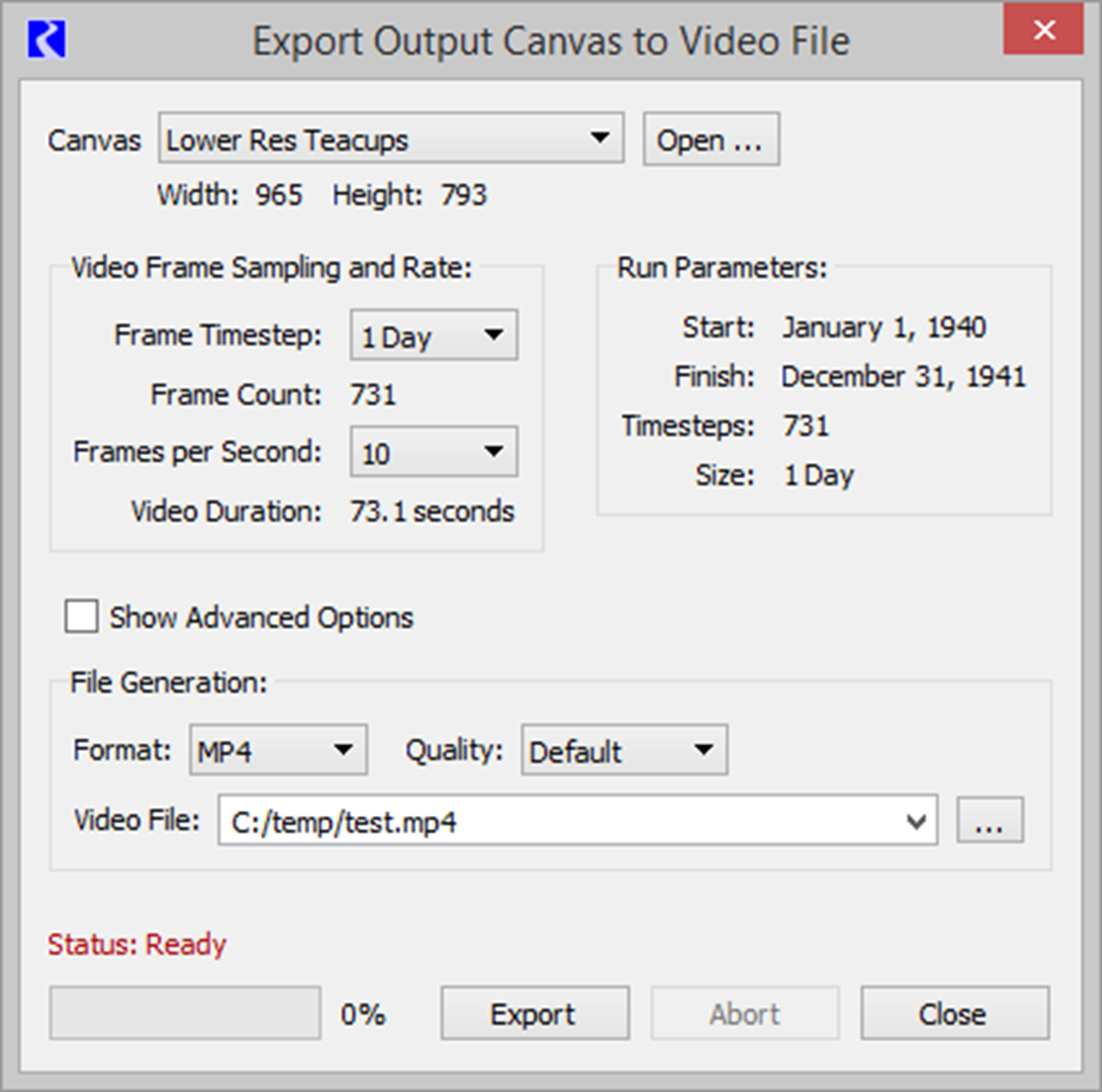
Chart
First specify the desired chart if it is not the one used to open the dialog. The height and width can be changed from the Chart Dialog, but not from this dialog.
Video Frame Sampling and Rate
In this area, you specify how the Chart animation is sampled including the timestep size to use and the speed of the animation in Frames per Second.
For reference, the right side shows the Run Parameters including Start and Finish Timesteps, number of timesteps in the run, and timestep size.
In the left portion, you select the timestep size, either the run timestep size or select a larger timestep size for sampling the animation. The total number of frames is computed based on the run parameters and the timestep size.
Also specify a frame rate for the animation. 5 frames per second is a good starting point.
The video duration is computed based on the frame count and frame rate.
File Generation
File generation can have complicated configuration options because of all the moving parts that must work together. As a result, the dialog provides two ways to configure the output file. The default basic configuration is usually sufficient for most users. Those who want more control over the options can Show Advanced Options to see advanced configuration.
Basic Configuration
The basic configuration provides three configuration options:
• Format: Select from one of the four supported formats. See Table 5.1 for descriptions of the formats and the quality.
• Quality: Select Default, Higher, Moderate, or Lower. This option is not available for GIFs or WEBM.
• Video File: Specify the file to create. Either type it in (include the file extension) or use the file chooser to navigate to the desired directory.
Format | Description and usage |
|---|---|
MP4 | This format displays well in PowerPoint and external players like widows media player. |
WEBM | This format works well when displayed in modern browsers like Firefox or Chrome. It cannot be shown in PowerPoint without an extension. |
WMV | This format displays well in PowerPoint and external players like widows media player. |
GIF | This format is very simple and shows the images repeating over and over, usually in a browser. There are no controls to start/stop/pause the video. Image quality is not as good as other options |
Advanced Options
When you select Show Advanced Options, you have full control over all aspects of the video file generation. Following are descriptions of the elements of advanced configuration.
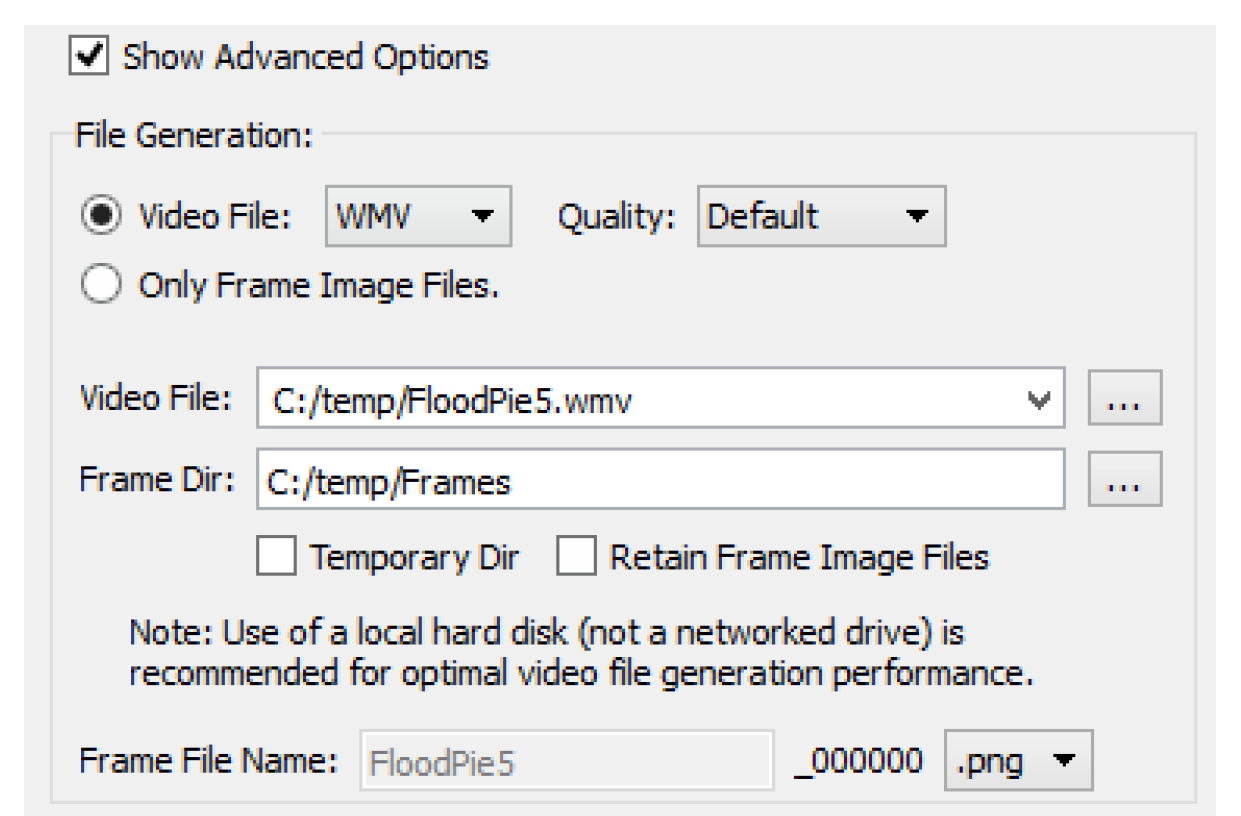
1. Choose whether you want to generate a Video File or generate only the Frame Image Files.
– Video File: Select the Video File format and Quality. See Table 5.1 for descriptions of the formats and the quality.
– Only Frame Image Files: The utility will create only image files at each timestep. They will not be combined into a video file. This option is useful if you have an alternative program that you want to use to assemble the images into a video. When this option is selected, there is no need to specify a Video File name.
2. Specify the location on the file system for the following:
– Video File: The location and name of the video file to create.
– Frame Dir: This shows the directory where the images files will be created. By default, this is the user’s temporary directory. If you deselect the Temporary Dir box, then you can specify any other directory.
3. If generating a video file, you can specify if you would like to retain the created image files by checking the Retain Image Frame Files. If not checked, they will automatically be deleted after the video file generation is complete.
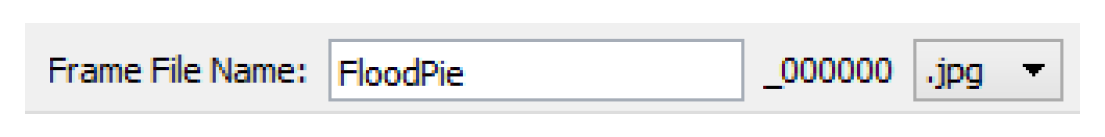
4. If you have selected Only Frame Image Files described above, you can also specify an alternative filing naming convention in the Frame File Name field. You can also choose to use JPG or PNG files.
5. The lower half of the configuration has options for Video File Creation Program Command. This optional panel allows you to further tweak or modify the arguments and commands that are passed to the external program. You can specify either or both of the following elements.
– Extra Global and Input File Options: These options are added to the input side, before the image files are specified. No further information is provided on available options.
– Extra Output File Options: These options are added on the output side, right before the output file specification. No further information is provided on available options.
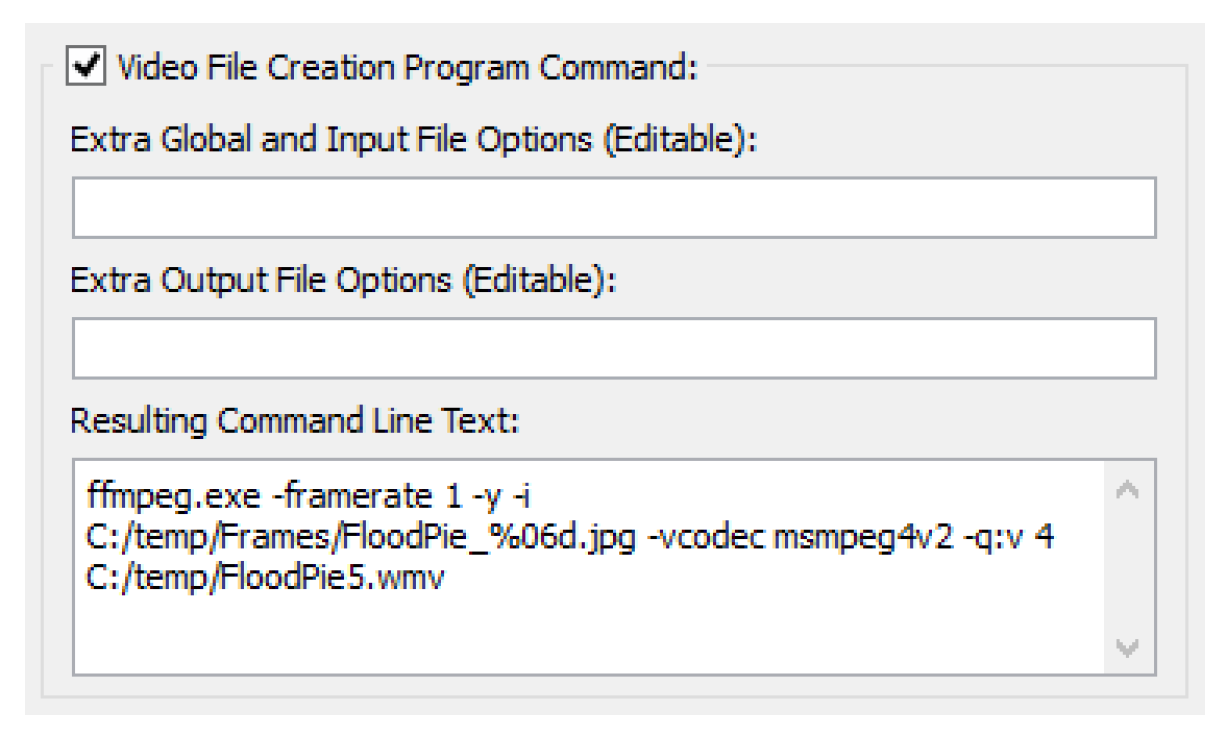
6. The resulting command line is shown in the Resulting Command Line Text field. This shows you exactly what will be executed. Copy is available if necessary.
Creating the Video File
When you choose to create the file by selecting Export, a dialog shows a confirmation before starting the generation. You should not close or resize the Chart dialog during video file generation or the process will be terminated.
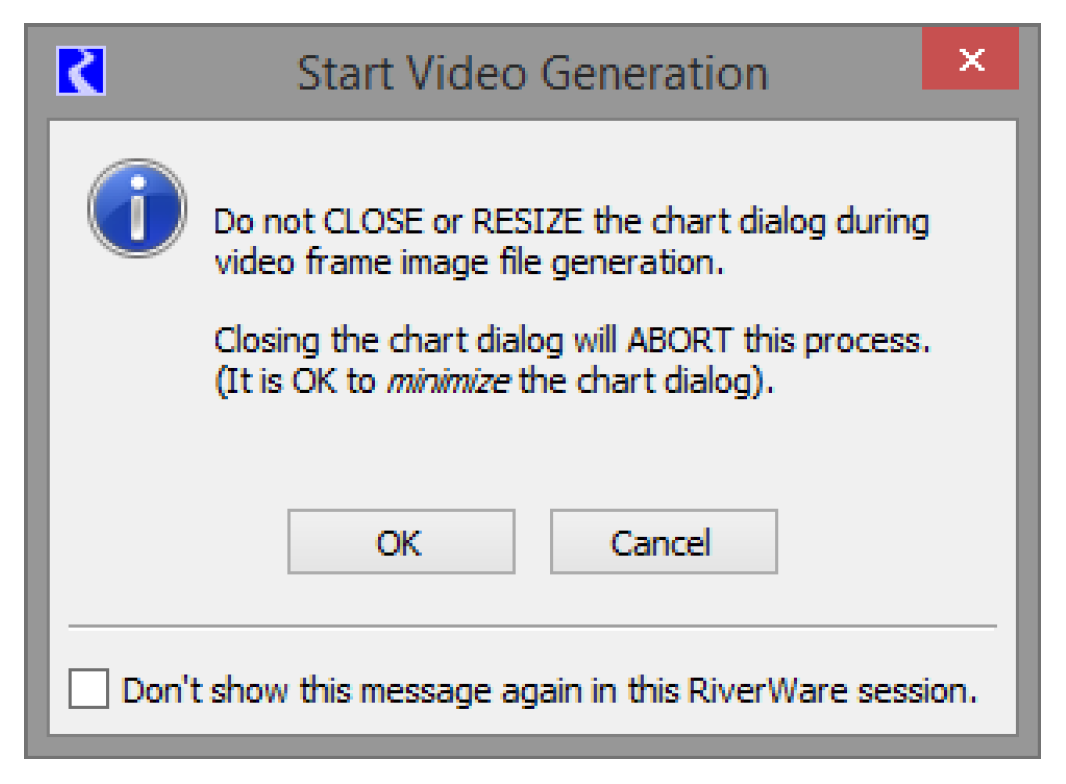
Select OK to generate the video file. The dialog shows the status of the export.
When finished, it shows the following status.
You can now navigate to the directory where the file was exported and view the file in the appropriate application. In addition, a log file is produced in that same directory with further debugging information on the generation process.
Revised: 08/02/2021